
Here is what you need to know to run a safe proxy business:
- Any proxy sale involves data processing, making you legally responsible for it.
- Following personal data protection laws prevents serious issues with law enforcement.
- iProxy.online acts as a secure Data Processor to help you handle logs correctly.
- You need to show legal terms to your clients, even when selling via chat.
- The safest strategy is keeping only essential contacts to maintain personal data security.
iProxy provides its clients with a unique infrastructure that enables the creation of their own mobile proxy servers. We strive for maximum convenience and personal data security online for a broad range of users, emphasizing the importance of clients being able to share their proxy accesses.
However, distributing proxy accesses to third parties entails the need to process their personal data. In this article, we will examine the key aspects that every seller should consider when dealing with personal data.
I Don't Collect Any Data, I Don't Even Have a Website – Why Do I Need This Information?
If you are simply providing proxy access to other people and not collecting any information about them, then the requirements of personal data legislation will not apply to you.
However, we strongly recommend not doing this, as it poses significant risks for you. For instance, if someone uses your phone's IP address to commit fraudulent actions, you could face serious problems with law enforcement authorities.
To minimize your risks, we recommend you keep contact details of users, such as email, phone numbers, and logs (read here about why we keep logs).
Next, we will explain how to do this correctly.
Need private and fast mobile proxies?Make mobile proxies right now!
How is the Processing of Personal Data Regulated?
Each country has its own legislation concerning personal data, and approaches to regulation can differ significantly from one another. For example, in Europe, unlike in the USA and Russia, where security services have relatively broad access to data, the personal data privacy of an individual is of paramount importance.
It is impossible to cover all approaches, so we will focus on the General Data Protection Regulation (GDPR) of the EU, as it is one of the strictest and covering many users.
GDPR is a document that regulates and standardizes the rules for the protection of personal data, applicable in the European Union (EU). You fall under its jurisdiction if you provide services to EU residents, even if you are located in another country.
What Constitutes Personal Data According to GDPR?
The GDPR does not provide a specific list of information that constitutes personal data. Essentially, it is any information that can be used to identify a Data Subject. Common personal data examples include a name, an identification number, location data, an online identifier (like an IP address), or email.
Among such data, GDPR identifies special categories of personal data, the processing of which requires additional protection measures. These include information like political and religious beliefs; health status; racial or ethnic origin; genetic and biometric data. These are often referred to as sensitive personal data.

What is Personal Data Processing?
Processing encompasses various actions with personal data – collection, recording, organization, storage, adaptation, alteration, retrieval, use, disclosure, dissemination, erasure, and so forth. Essentially, if you have simply become aware of someone's personal data, its processing has already begun.
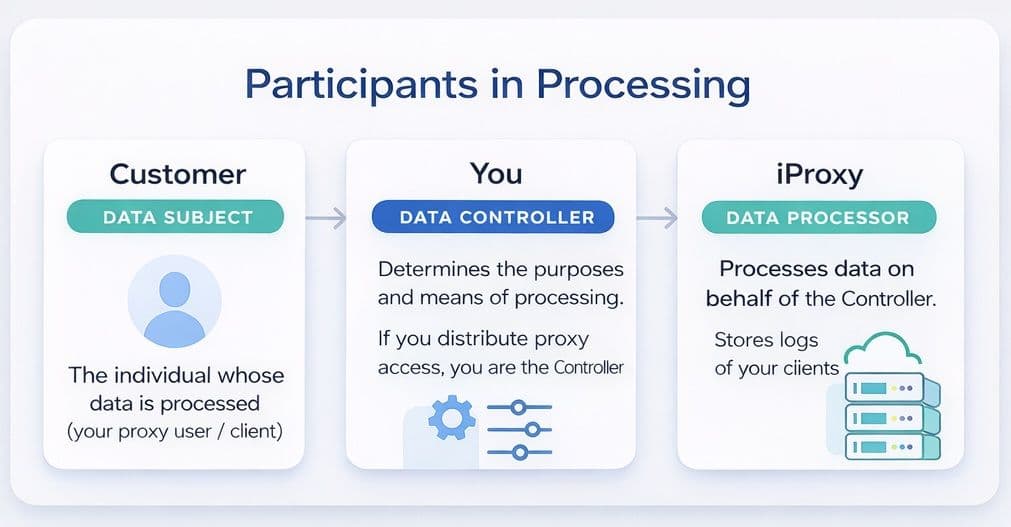
Who is Involved in the Processing of Personal Data?
- Data Subject – the individual whose data is being processed. In your case, this is the user of your proxy access (your "Customer").
- Data Controller – the entity that determines the purposes and means of processing personal data. If you distribute proxy access to your clients, you are the Data Controller for their information.
- Data Processor – the entity that processes data on behalf of the Data Controller. When you distribute proxy access to your clients, we act as the data processor for personal data and carry out processing, which involves storing logs of your clients.
Cases Where You May Process Personal Data:
- The Data Subject has given consent to the processing of their personal data.
- The processing is necessary for the performance of a contract.
- The processing is necessary for compliance with a legal obligation imposed on the Data Controller.
- The processing is necessary to protect the vital interests of the Data Subject.
- The processing is necessary for the purposes of the legitimate interests pursued by the Data Controller or by a third party.
In any other cases, you cannot process user data.
If you store only contact details and user logs, as we recommend, the basis for processing personal data will be your legitimate interest, which is expressed in protecting against the risk of fraudulent activities by clients.
GDPR mandates that only the minimum necessary information should be stored, so if you need to save any additional information, you must identify a suitable basis for this. However, please note that if you are relying on user consent for the collection and processing of personal data, it must be explicit. A pre-checked box in the field "I agree to the collection and processing of personal data" is considered a violation.
What documents will I need?
Privacy Policy
You need to develop and publish a Privacy Policy. It should specify the purposes, methods of collection, and processing of personal data, as well as information about to which third parties and for what purposes users' personal data may be transferred.
If you do not have a website where this information can be posted, we recommend you do the following:
Create a template message in a messenger app that you can send to users. Briefly outline in it the main information about tariffs and refund terms and conditions.
Include in this message:
- A link to the text of the Terms of Service. These should detail the specific terms of the service, including refund conditions.
- A link to the text of the Privacy Policy. This document should describe the process of personal data processing.
For your convenience, we have prepared templates of the necessary documents, which you can download and customize. Terms of Service template, Privacy Policy template
You must provide these two documents to your clients before starting work with them, and you also need to obtain explicit consent that they are informed and agree with all these documents.
Record of Processing Activities
Every Data Controller is required to maintain a Record of Processing Activities (RoPA). This is usually a table in an Excel format. In RoPA, it is necessary to record, in particular, the purposes of processing, description of the categories of personal data subjects, description of the categories of persons to whom personal data is transferred, etc.
This document will be useful for you to clearly understand what and how you are processing, as well as in case your client requests information about how you store the data.
Data Protection Agreement (DPA)
A Data Protection Agreement (DPA) is a legally binding document entered into between the data controller and the data processor in the context of the processing of personal data. It outlines the scope, nature, and purpose of processing, the rights and obligations of both parties, and compliance measures with applicable data protection laws, most notably the General Data Protection Regulation (GDPR) for entities operating within or dealing with data from the European Union.
If you are distributing proxies created using our infrastructure, please email us at [email protected], and we, as a data processor, will send you an agreement to sign.
How Should I Organize Data Storage to Ensure Compliance?
You can store the contact details of your users in any form, for example, in a table. The main requirement is that no one except you should have access to this information.
As data processor, we store anonymized logs of your users on our servers, which are securely protected against leaks.
Under GDPR, it is required to implement technical and organizational measures to prevent information leaks. If a leak is detected, data subjects must be notified without delay.
When and to Whom Can Personal Data Be Disclosed?
Personal data can be disclosed only in the following cases:
- If required by law or in response to justified requests from government authorities, you may be required to disclose personal data of your clients. When receiving such a request, always verify its legitimacy.
- To contractors, service providers, and other third parties whom you use to support your business, but information about this should be reflected in your privacy policy.
- In any other cases with the consent of the client.
Please note that selling personal data is permissible only with the direct consent of the client.
Risks of Violating GDPR
For breaching GDPR regulations, companies face a multi-tiered fine system depending on the severity of the violation:
- Level 1: 2% of the global turnover or €10 million.
- Level 2: 4% of the global turnover or €20 million.
For example, on the first day of the regulation's enforcement, Google and Facebook faced lawsuits totaling $8.8 billion.
Of course, if the scale of your business is smaller than that of Google, the chances of regulatory authorities noticing you are not as high. However, it is never possible to completely rule out the risk of having a client who, for some reason, might complain about you to the authorities, compelling them to investigate your resources.
Conclusion
Proper handling of your clients' personal data is not just a legal requirement, but also a key element for your own safety.
At iProxy, we take this aspect seriously and provide you with all the tools and knowledge you need for effective and secure operations. If you're just starting and want to dive deeper into the technical side and learn what is mobile proxy farm, or need advice on a stable mobile proxy farm setup, we have plenty of materials to help you. We strictly adhere to rigorous standards in processing and personal data protection to ensure that both you and your clients remain safe.
- Best Mobile Proxy Providers [2026]
- How to Set Up Remote Change of IP Address Through iProxy.online?
- How to Make Money With Proxies [The Complete Guide]
- How to Increase the Proxy Speed: Detailed Guide
- Guide for setting up mobile proxies in iProxy.online
- All about .OVPN configs, UDP, HTTP/3, QUIQ support
- What is Wi-Fi Split? How does it help to increase the speed and reduce traffic consumption?
- Replace passive OS fingerprint in mobile proxies
- List of recommended phones for iProxy.online
- How to choose the right location of the server?
Do proxy sellers need to comply with data protection laws?
Yes. If you provide access to EU residents, you must adhere to GDPR regulations regarding personal data protection. Even without a website, simply collecting user contacts or logs makes you a Data Controller liable for compliance.
How should proxy sellers store and protect user data?
Store minimal data (contacts/logs) securely where only you have access to ensure personal data security. iProxy.online helps by storing anonymized logs on secure servers as a Data Processor, reducing your technical burden.
Can proxy sellers track users without violating privacy?
Tracking requires a legal basis. Storing logs for fraud prevention is a legitimate interest, but maintaining personal data privacy requires you to inform users via a Privacy Policy
- Best Mobile Proxy Providers [2026]
- How to Set Up Remote Change of IP Address Through iProxy.online?
- How to Make Money With Proxies [The Complete Guide]
- How to Increase the Proxy Speed: Detailed Guide
- Guide for setting up mobile proxies in iProxy.online
- All about .OVPN configs, UDP, HTTP/3, QUIQ support
- What is Wi-Fi Split? How does it help to increase the speed and reduce traffic consumption?
- Replace passive OS fingerprint in mobile proxies
- List of recommended phones for iProxy.online
- How to choose the right location of the server?
